Connecting an Oracle Cloud Infrastructure (OCI) account
Overview
To onboard your OCI environment to DigiUsher, an IAM user with read-only access to cost, usage, resource, and metrics data is required. This document describes exactly what permissions are requested, why each is needed, and what credentials to provide.
OCI is FOCUS ready — DigiUsher fetches Cost and Usage Reports from the FOCUS Cost Report Schema.
Summary of Access Required
| Component | Details |
|---|---|
| Identity | OCI IAM User (digiusher-service-user) — API-only, no Console password |
| Authentication | API key pair (PEM private key + fingerprint) |
| Access level | Read-only — all policies use the read verb only |
| Scope | Tenancy-wide |
| Billing | Read-only access to cost and usage reports |
| Data access | Cost and Usage Reports via Oracle's cross-tenancy bucket (FOCUS format only) |
| Capability | What It Provides |
|---|---|
| Billing data | Cost analytics, chargeback/showback, budgeting, forecasting, anomaly detection |
| Resource inventory | Asset discovery, idle resource detection, tag-based cost allocation |
| Optimization recommendations | Rightsizing, commitment analysis, idle resource cleanup |
| Utilization metrics | CPU, memory, network, disk usage for rightsizing analysis |
DigiUsher cannot create, modify, or delete any of your OCI resources.
Use Terraform or OCI Resource Manager for the fastest setup
We strongly recommend the DigiUsher Terraform configuration for the most efficient and reliable setup. It automates the entire process in ~2 minutes.
You can also deploy with one click using OCI Resource Manager — no local tools required.
Terraform Repository: https://github.com/digiusher/digiusher-iac/
If your organization's policies require manual resource provisioning, follow the steps below.
Prerequisites
Information to Gather
| Item | How to Find |
|---|---|
| Tenancy OCID | OCI Console > Administration > Tenancy Details |
| Home Region | e.g. us-ashburn-1 — shown in Tenancy Details |
Roles Required by the Person Performing Setup
| Role | Why |
|---|---|
| Tenancy Administrator | To create IAM users, groups, and policies |
Network & Email Access (For Regulated Environments)
If your organization restricts outbound internet access or email domains, ensure the following are in place before starting:
- Domain allowlist: Add
*.digiusher.comto your network/firewall allowlist so that users in your organization can access the DigiUsher platform from their browsers. - Email allowlist: Add
digiusher.comas an approved sender domain in your email security gateway. DigiUsher sends onboarding confirmations, alerts, and reports from@digiusher.comaddresses.
Option A: Terraform (Recommended)
One-Click Deploy via OCI Resource Manager
- Click the button above (you'll be redirected to the OCI Console)
- Log in to your OCI tenancy
- Review the pre-filled configuration and adjust if needed
- Click Create to deploy the stack
- Wait for the stack to complete (~2 minutes)
- Continue to After Terraform or ORM Deploy
Local Terraform
git clone https://github.com/digiusher/digiusher-iac.git
cd digiusher-iac/oci
terraform init
terraform plan -var="tenancy_ocid=<your-tenancy-ocid>" -var="region=<your-region>"
terraform apply -var="tenancy_ocid=<your-tenancy-ocid>" -var="region=<your-region>"After Terraform or ORM Deploy
Generate an API Key
This step cannot be automated. See Step 4: Generate API Key below.
Connect in DigiUsher
Enter the credentials into the DigiUsher platform (see Connect in DigiUsher below).
See the digiusher-iac README for full Terraform documentation including parameters, feature flags, and troubleshooting.
Option B: Manual Setup
Follow these steps if you prefer to set up via the OCI Console.
Step 1: Create IAM Group
- Go to OCI Console > Identity > Domains
- Select Default domain
- Go to User Management > Groups
- Click Create Group
- Configure:
- Name:
digiusher-finops-group - Description:
DigiUsher FinOps platform - read-only access for cost analytics and optimization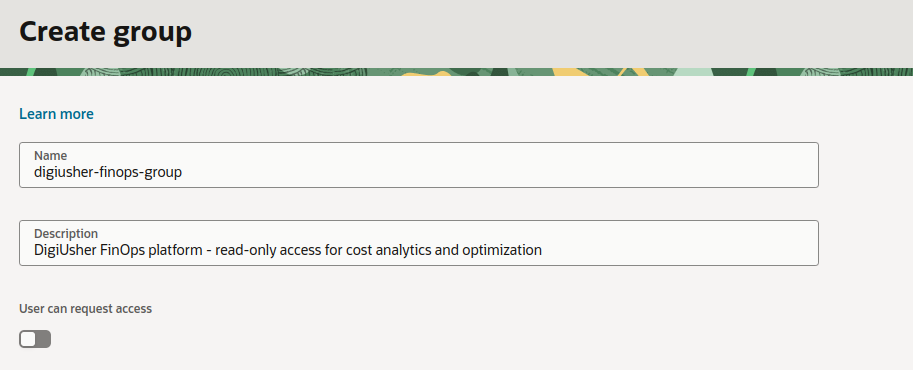
- Name:
- Click Create
Step 2: Create IAM User
- Go to OCI Console > Identity > Domains
- Select Default domain
- Go to User Management > Users. Click on Create.
- Configure:
- Name:
digiusher-service-user - Description:
Service user for DigiUsher FinOps platform - Email (required by OCI): Use something like
digiusher-svc-oci@YOUR_COMPANY_NAME.com
- Name:
- Add the user to the
digiusher-finops-groupwe created in the previous step.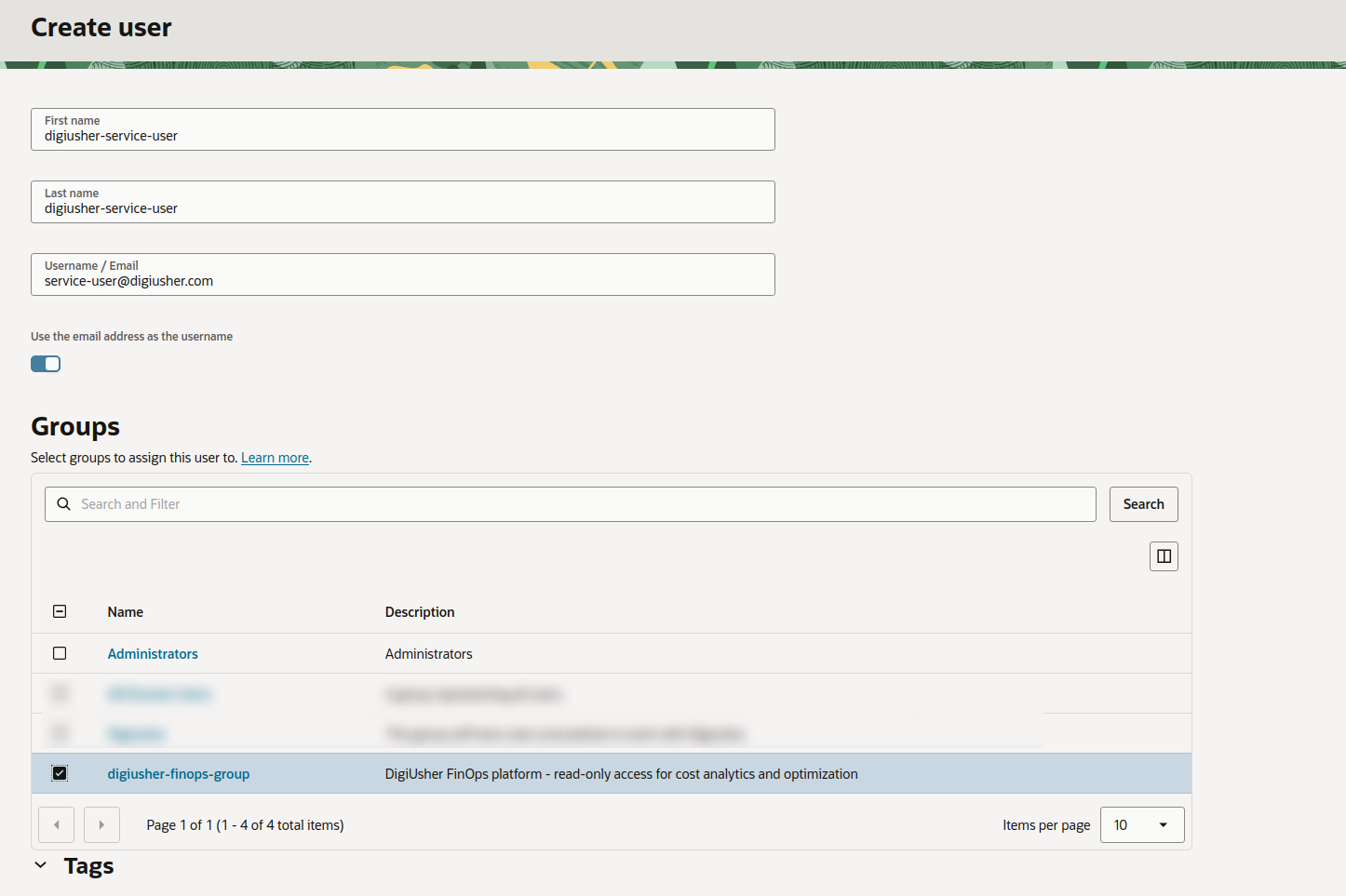
- Click Create
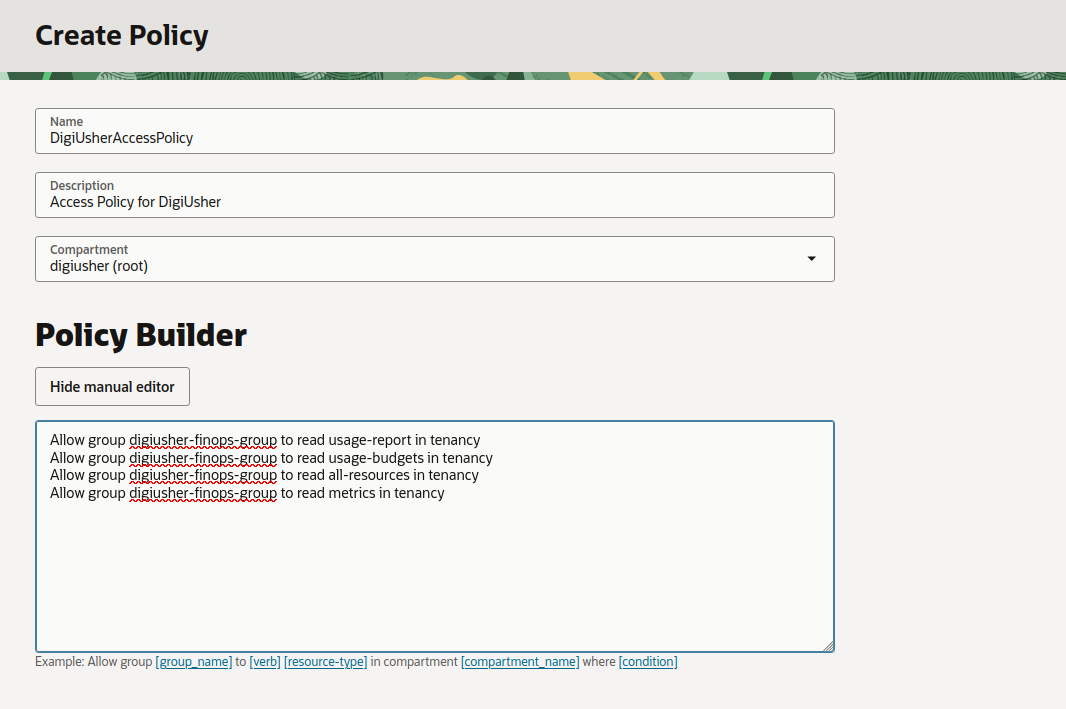
Step 3: Create IAM Policies
Create the following two policies under Identity > Policies > Create Policy.
For each policy, set Compartment to your root compartment (tenancy level).
OCI requires define/endorse statements to be in a separate policy from Allow statements. Create the following two policies at the tenancy (root compartment) level.
Policy 1: Cost Report Cross-Tenancy Access
Grants read access to Oracle's cost reporting tenancy for FOCUS cost reports. The OCID below is Oracle's cost reporting tenancy — it is the same for all OCI customers.
define tenancy usage-report as ocid1.tenancy.oc1..aaaaaaaaned4fkpkisbwjlr56u7cj63lf3wffbilvqknstgtvzub7vhqkggq
endorse group digiusher-finops-group to read objects in tenancy usage-reportPolicy 2: DigiUsher Access Policy
Grants read access to usage reports, budget data, resource metadata, and monitoring metrics.
Allow group digiusher-finops-group to read usage-report in tenancy
Allow group digiusher-finops-group to read usage-budgets in tenancy
Allow group digiusher-finops-group to read all-resources in tenancy
Allow group digiusher-finops-group to read metrics in tenancyAll policies are strictly read-only. Nothing can be modified, deleted, or created in your environment.
Note
If you leave out the last two statements (all-resources and metrics), DigiUsher will not be able to provide optimization recommendations, rightsizing suggestions, or utilization-based insights.
Below is a screenshot showing the policy creation in the OCI Console. Click Create Policy, fill in the name, description, set compartment to root, switch to the manual editor, and enter the policy statements:
Step 4: Generate API Key
This step applies to both Option A and Option B. API key generation cannot be automated.
- Go to OCI Console > Identity > Users
- Click on
digiusher-service-user(or the name you configured)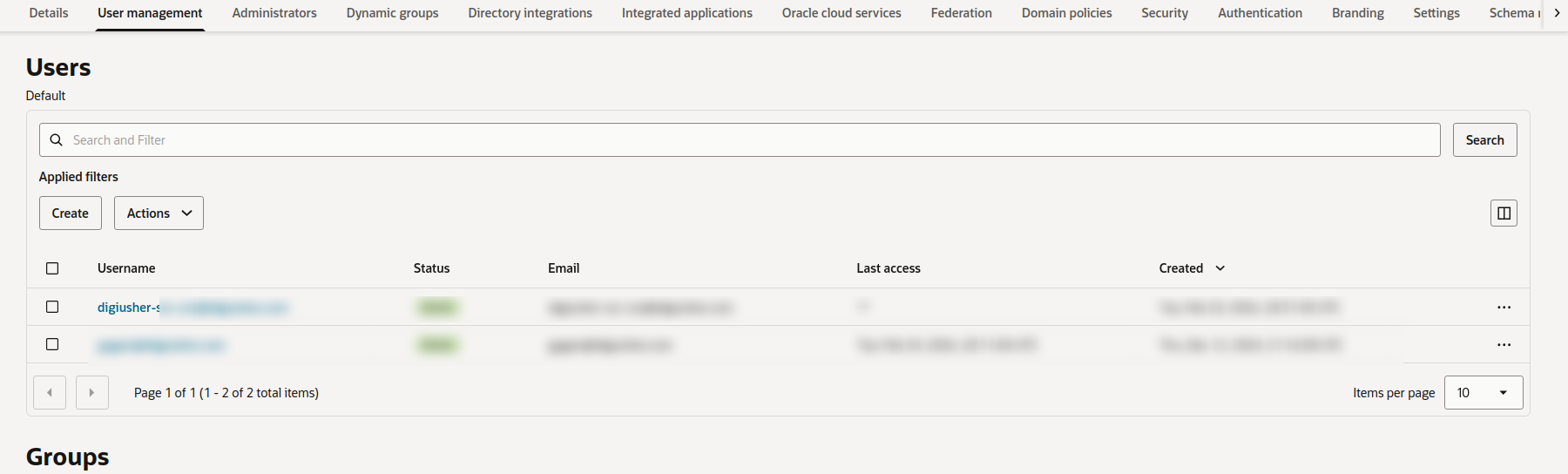
- Under Resources, click API Keys
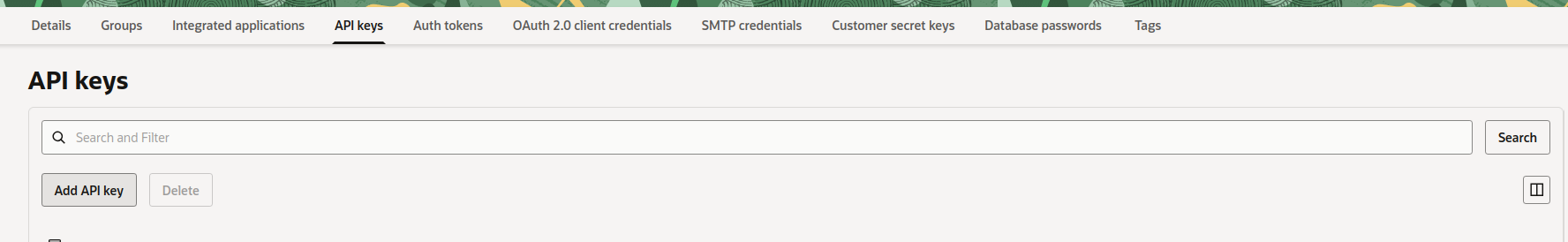
- Click Add API Key
- Select Generate API Key Pair
- Click Download Private Key and save the
.pemfile securely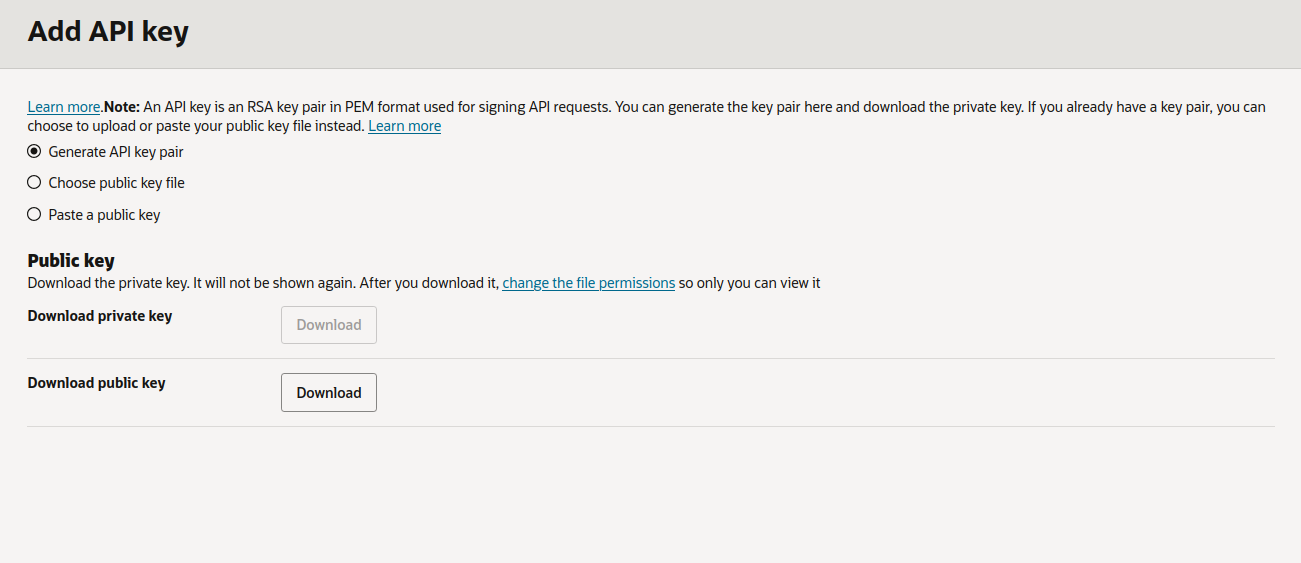
- Click Add
- A Configuration File Preview will be displayed with user OCID, fingerprint, tenancy OCID, and region. Save these details by clicking the copy button.
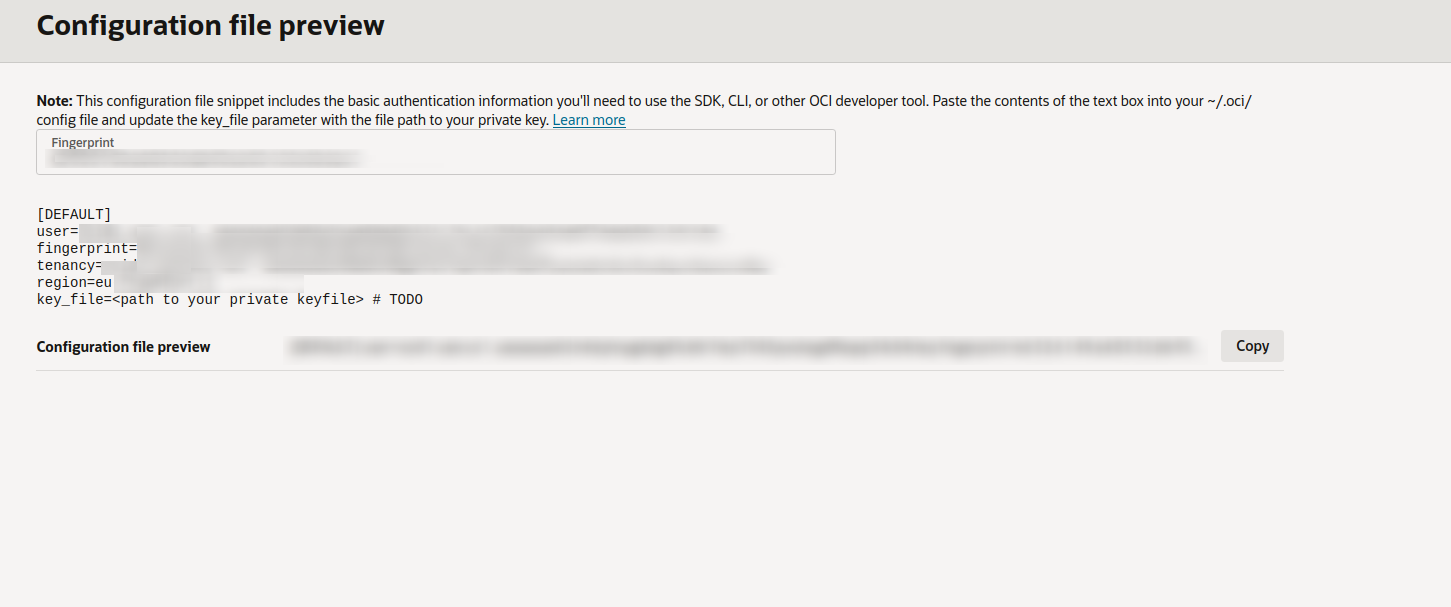
Important
The private key is only shown once. Store it securely.
Connect in DigiUsher
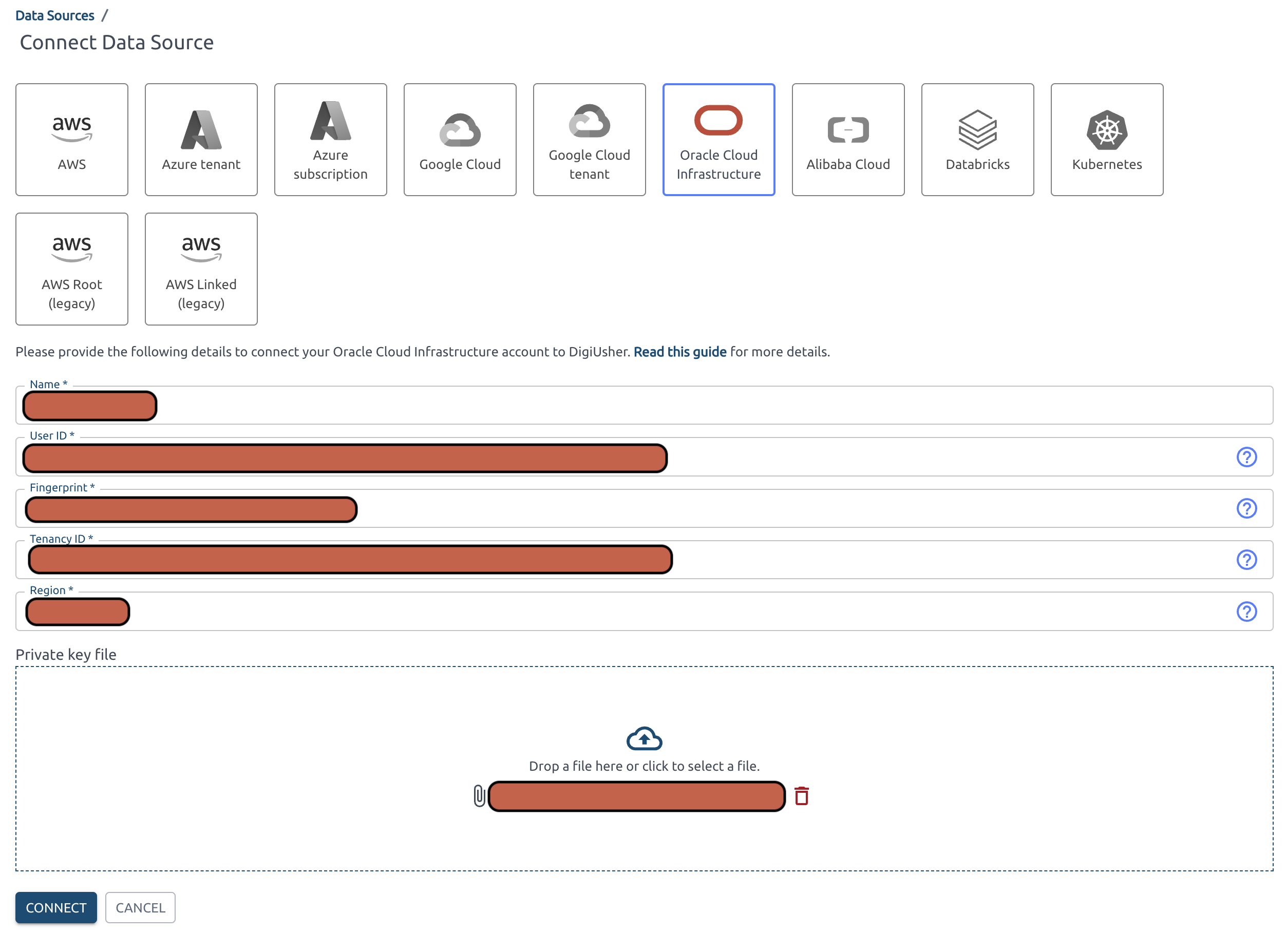
After completing either Option A or B, enter the following into the DigiUsher platform to complete the connection:
| Field | Where to Find |
|---|---|
| Tenancy OCID | OCI Console > Administration > Tenancy Details |
| User OCID | Terraform output or OCI Console > Identity & Security > Users > digiusher-service-user |
| Home Region | e.g. us-ashburn-1 — shown in Tenancy Details |
| API Key Fingerprint | Displayed after adding the API key (Configuration File Preview) |
| Private Key (PEM) | Contents of the downloaded .pem file |
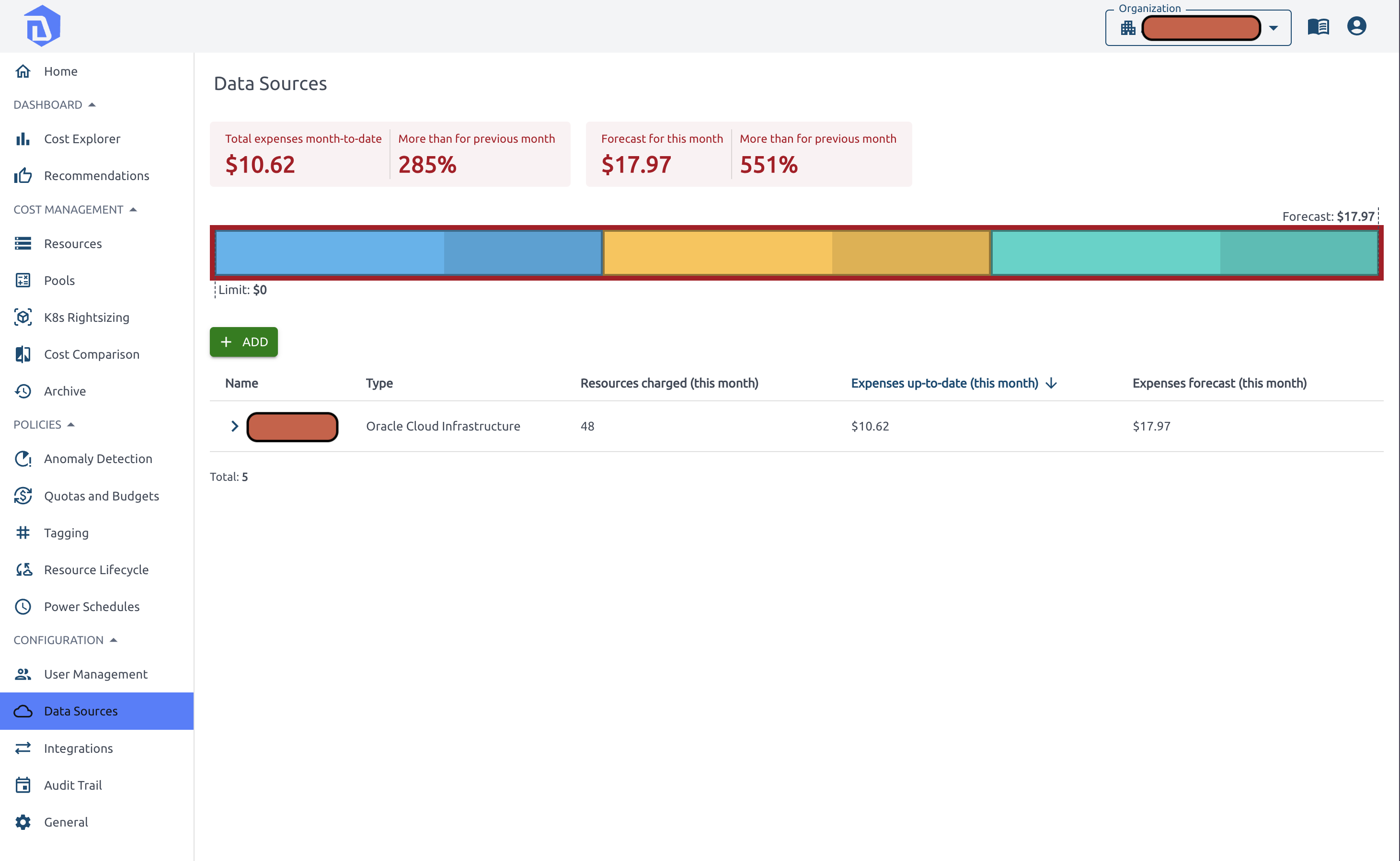
Adding the Data Source
-
Go to the DigiUsher navigation menu > Data Sources. If you are a new user, click Connect Data Source.
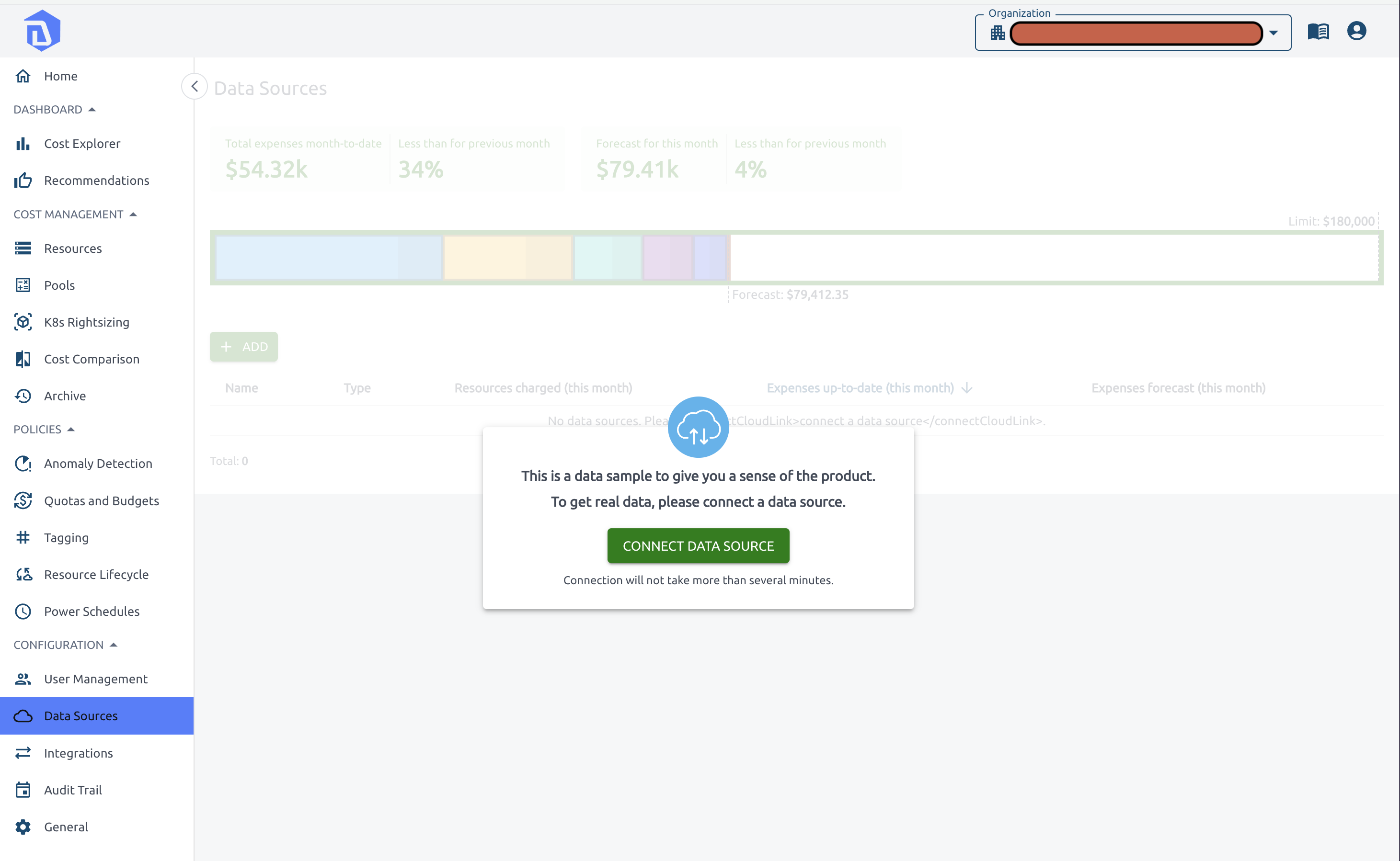 If you have already added a data source previously, click Add.
If you have already added a data source previously, click Add.
-
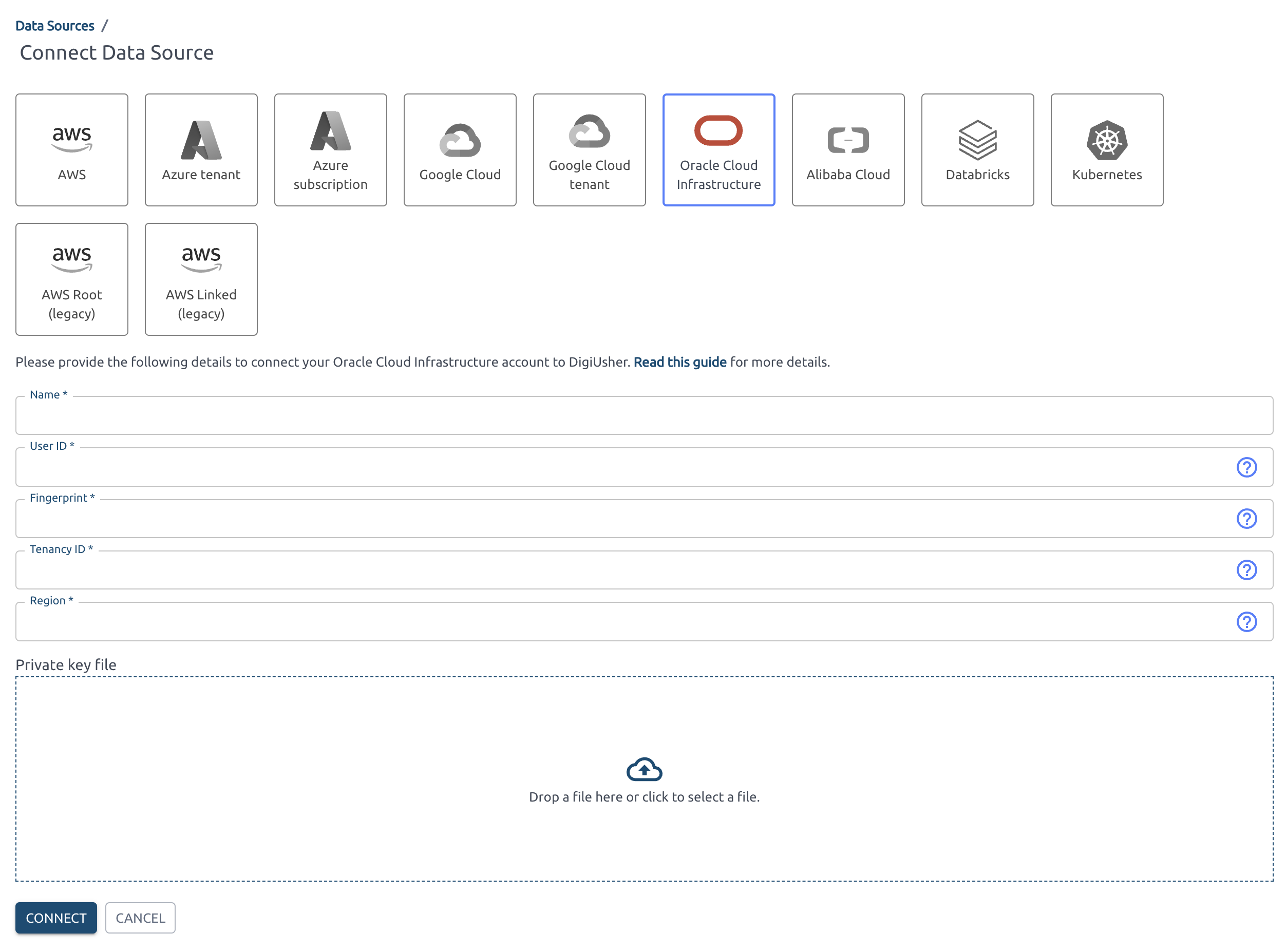
Select Oracle Cloud Infrastructure as the data source type.
-
Enter the details from the Configuration File Preview you saved earlier.
-
Upload the private key
.pemfile. -
Click Connect.
Verification Checklist
- IAM group
digiusher-finops-groupcreated - IAM user
digiusher-service-usercreated and added to the group - Policy 1: cost report cross-tenancy endorse created
- Policy 2: DigiUsher access policy created
- API key generated and private key saved
- All 5 credential values entered into the DigiUsher platform
-
*.digiusher.comallowlisted in network/firewall (if applicable) -
digiusher.comallowlisted for incoming email (if applicable)
Security
What DigiUsher CAN Access (Read-Only)
- Cost and usage reports (FOCUS format) via Oracle's cross-tenancy bucket
- Budget data
- Resource metadata (names, types, regions, tags) via Resource Search API
- Utilization metrics (CPU, memory, network, disk) via OCI Monitoring
- Organization and compartment hierarchy
What DigiUsher CANNOT Do
- Create, modify, or delete any OCI resources
- Access application data, databases, or storage contents
- Modify IAM policies or permissions
- Read secrets, credentials, or encryption keys
- Access network traffic or logs content
- Make purchases or modify billing settings
Monitoring
Monitor service account activity in OCI Console > Identity & Security > Audit, filtering by user digiusher-service-user.
Credential Rotation
- Terraform:
terraform apply -replace="oci_identity_api_key.digiusher" - Manual: Go to Identity & Security > Users > digiusher-service-user > API Keys > Add API Key (generate new), then delete the old key. Enter the new key details into the DigiUsher platform.
Revocation
- Terraform:
terraform destroy— removes the user, group, all policies, and invalidates the API key. - OCI Resource Manager: Go to Developer Services > Resource Manager > Stacks > select the DigiUsher stack > Destroy.
- Manual: Delete the
digiusher-service-useruser in Identity & Security > Users. This instantly invalidates the API key and associated group membership. Then remove thedigiusher-*policies.
Troubleshooting
"Authorization failed" when creating policies
You need tenancy administrator access. Ensure you are logged in as an administrator or have manage permissions on users, groups, and policies.
"Policy statement is invalid"
The cross-tenancy endorse and define statements must be in a separate policy from Allow statements. Verify that Policy 1 statements are not mixed with those in Policy 2.
DigiUsher reports "Unable to access cost reports"
- Verify the
endorsepolicy exists under Identity & Security > Policies - Ensure the API key fingerprint matches what's configured in DigiUsher
- Confirm the private key PEM content was copied completely (including
-----BEGINand-----ENDlines) - Cost reports may take up to 24 hours to appear for new tenancies
Memory metrics not available
Memory metrics require the Oracle Cloud Agent with the Compute Instance Monitoring plugin enabled on your instances. This is enabled by default on most platform images but may need manual activation on custom images.
Need Help?
If you encounter any issues not covered above, contact us at support@digiusher.com and we'll help you get set up.
 DigiUsher Documentation
DigiUsher Documentation