Connecting an Azure account (Enterprise Agreement)
Overview
To onboard your Azure environment to DigiUsher, an App Registration with read-only access to cost, usage, and resource metadata is required. This document describes exactly what permissions are requested, why each is needed, and what credentials to provide. This guide covers Enterprise Agreement (EA) customers.
Summary of Access Required
| Component | Details |
|---|---|
| Identity | Azure App Registration (DigiUsherApp) — service principal, no interactive login |
| Authentication | Client secret (recommended 24-month expiry) |
| Access level | Read-only — Reader role at Management Group level |
| Scope | All subscriptions under the root Management Group |
| Billing | FOCUS cost export from Billing Account scope |
| Data access | Storage Blob Data Reader on the cost export storage account only |
| Capability | What It Provides |
|---|---|
| Billing data | Cost analytics, chargeback/showback, budgeting, forecasting, anomaly detection |
| Resource inventory | Asset discovery, idle resource detection, tag-based cost allocation |
| Optimization recommendations | Reservation and Savings Plan analysis, idle resource cleanup |
| Utilization metrics | Resource usage for rightsizing analysis |
DigiUsher cannot create, modify, or delete any of your Azure resources.
Use Terraform for the fastest setup
We strongly recommend the DigiUsher Terraform configuration for the most efficient and reliable setup. It automates the entire process and simplifies future maintenance.
Terraform Repository: https://github.com/digiusher/digiusher-iac/
If your organization's policies require manual resource provisioning, follow the steps below.
Prerequisites
Information to Gather
| Item | How to Find |
|---|---|
| Tenant ID | Azure Portal > Microsoft Entra ID > Overview |
| Billing Account ID | Cost Management + Billing > Billing scopes |
| Subscription ID | A subscription to host the storage account for cost exports |
Roles Required by the Person Performing Setup
| Role | Why |
|---|---|
| Global Administrator or Application Administrator | To create the App Registration and assign IAM roles |
| EA Admin | To assign billing roles and create cost exports at billing scope |
| Subscription Owner | To create storage resources for cost exports |
Network & Email Access (For Regulated Environments)
If your organization restricts outbound internet access or email domains, ensure the following are in place before starting:
- Domain allowlist: Add
*.digiusher.comto your network/firewall allowlist so that users in your organization can access the DigiUsher platform from their browsers. - Email allowlist: Add
digiusher.comas an approved sender domain in your email security gateway. DigiUsher sends onboarding confirmations, alerts, and reports from@digiusher.comaddresses.
Option A: Terraform (Recommended)
Our Terraform configuration automates the entire setup.
git clone https://github.com/digiusher/digiusher-iac.git
cd digiusher-iac/azure
cp terraform.tfvars.ea-enrollment-account-example terraform.tfvars
# Edit terraform.tfvars with your values
terraform init
terraform plan
terraform applySee the digiusher-iac README for full Terraform documentation including parameters and troubleshooting.
Option B: Manual Setup
Follow these steps if you prefer to set up via the Azure Portal.
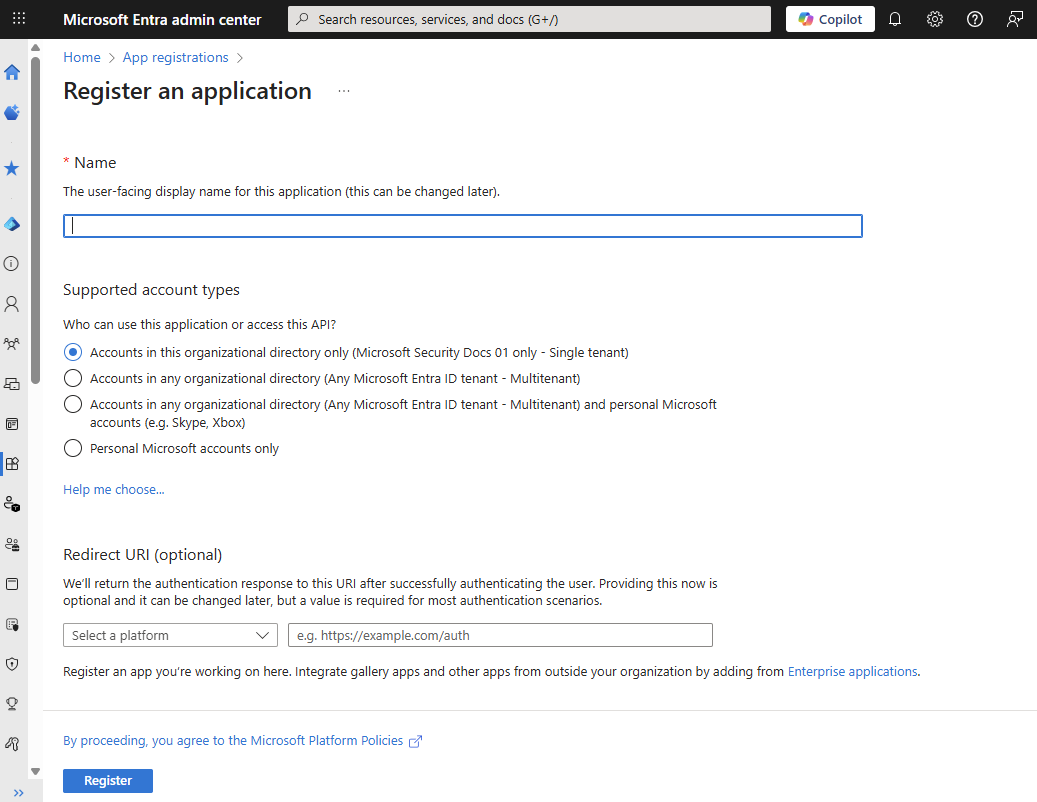
Create App Registration
- Go to Azure Portal → Microsoft Entra ID → App registrations
- Click New registration
- Configure:
- Name:
DigiUsherApp - Supported account types: "Accounts in this organizational directory only"
- Name:
- Click Register
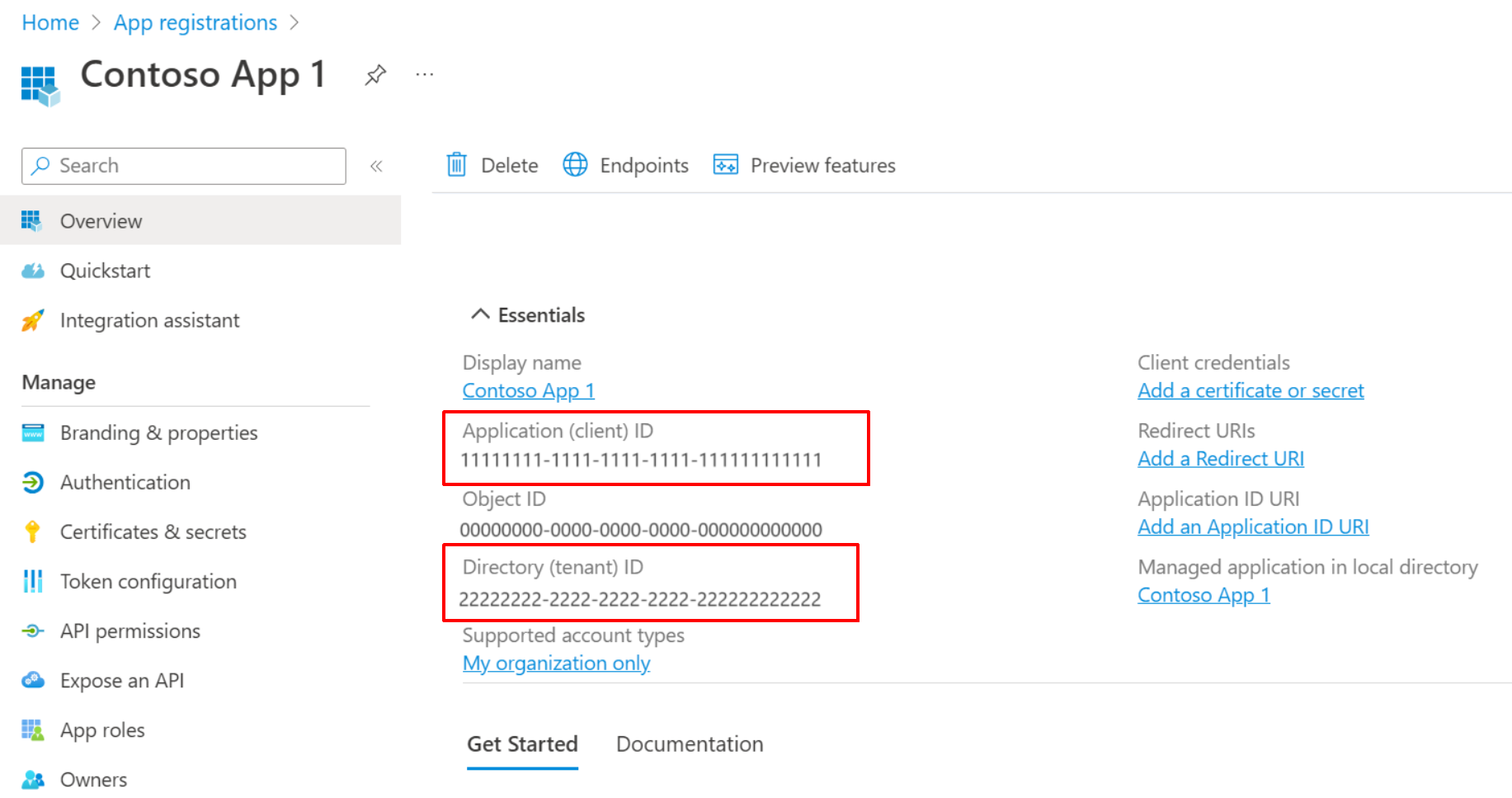
- Note down:
- Application (client) ID
- Directory (tenant) ID
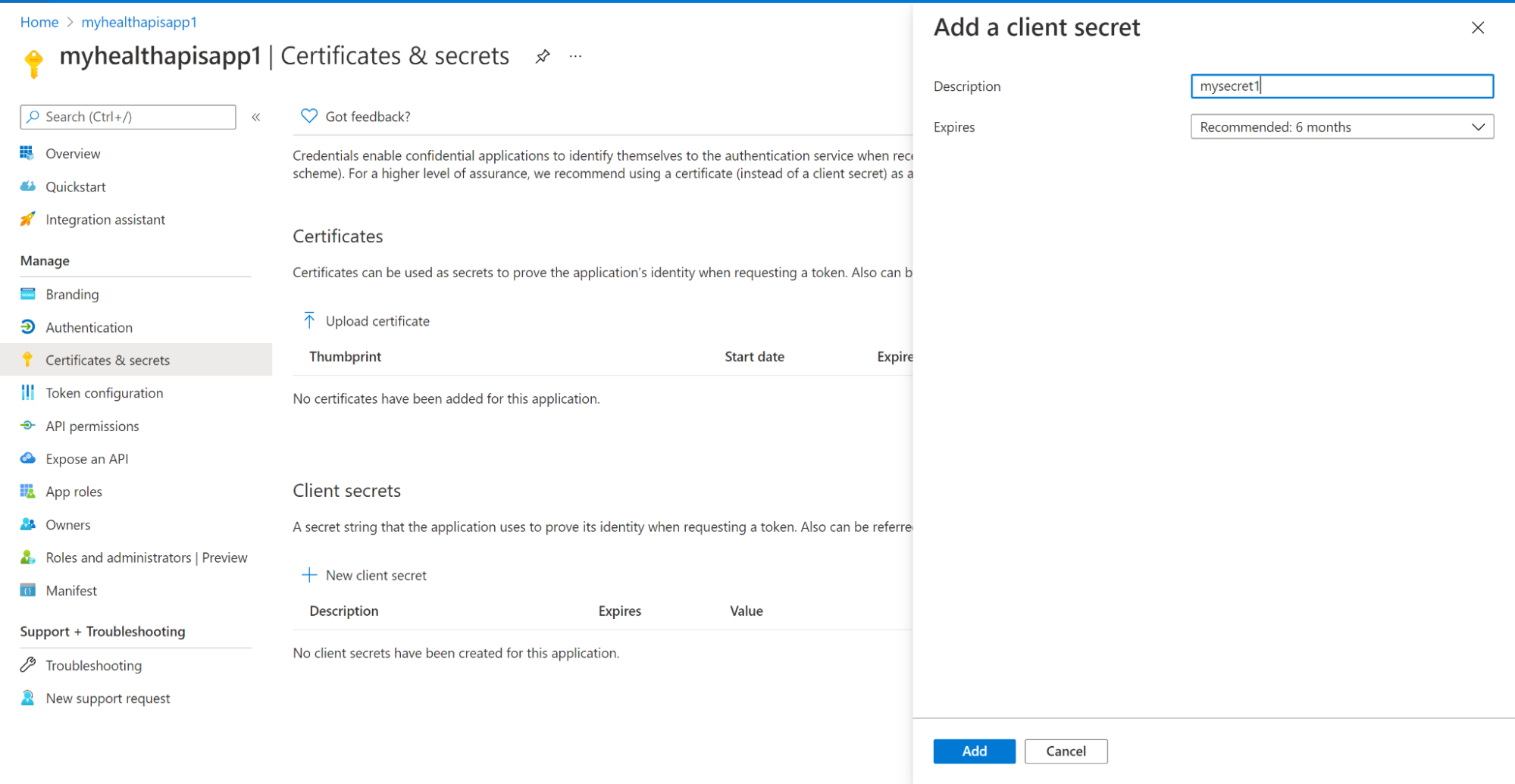
Create Client Secret
- In your app registration, go to Certificates & secrets
- Click New client secret
- Configure:
- Description:
DigiUsher secret - Expires: 24 months (recommended)
- Description:
- Click Add
- Copy the Value immediately — it won't be shown again
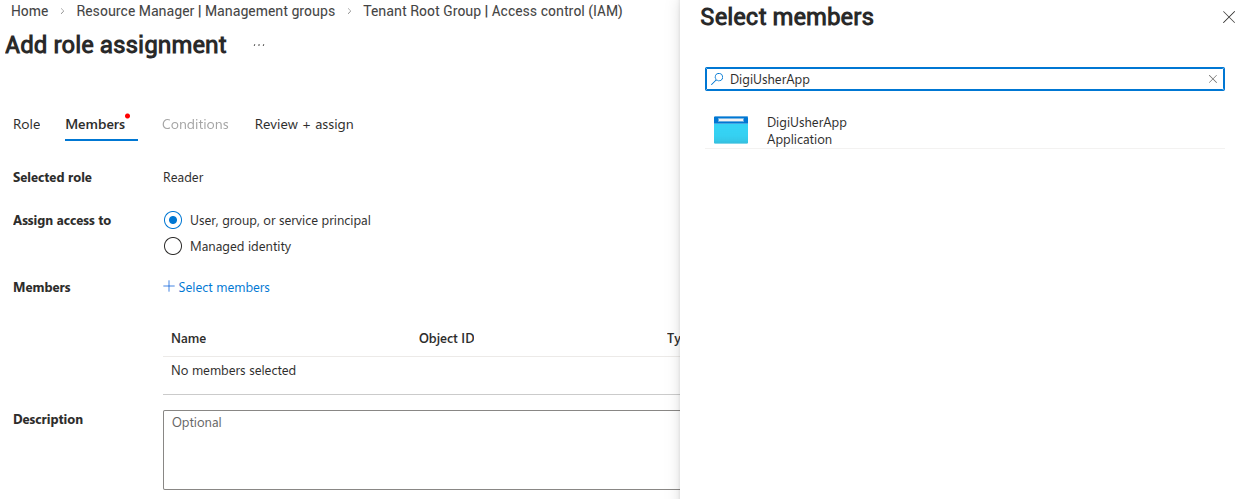
Assign Reader Role
- Go to Management Groups → Select your root management group
- Click Access Control (IAM) → Add → Add role assignment
- Configure:
- Role:
Reader - Members: Search for and select
DigiUsherApp
- Role:
- Click Review + assign
Note
Assigning at Management Group level covers all current and future subscriptions.
Create Storage Account for Exports
4a. Create Resource Group
- Go to Resource Groups → Create
- Configure:
- Name:
digiusher-billing-exports - Region: East US (or your preferred region)
- Name:
- Click Review + create → Create
4b. Create Storage Account
- Go to Storage accounts → Create
- Configure:
- Resource group:
digiusher-billing-exports - Storage account name: Something unique, lowercase alphanumeric only (e.g.,
digiusherexports<yourcompany>) - Region: Same as resource group
- Performance: Standard
- Redundancy: LRS (Locally-redundant storage)
- Resource group:
- Click Review + create → Create
4c. Create Container
- Open your new storage account
- Go to Containers → + Container
- Configure:
- Name:
digiusher-focus-exports - Public access level: Private
- Name:
- Click Create
4d. Grant Storage Access
- On the storage account, go to Access Control (IAM) → Add → Add role assignment
- Configure:
- Role:
Storage Blob Data Reader - Members: Search for and select
DigiUsherApp
- Role:
- Click Review + assign
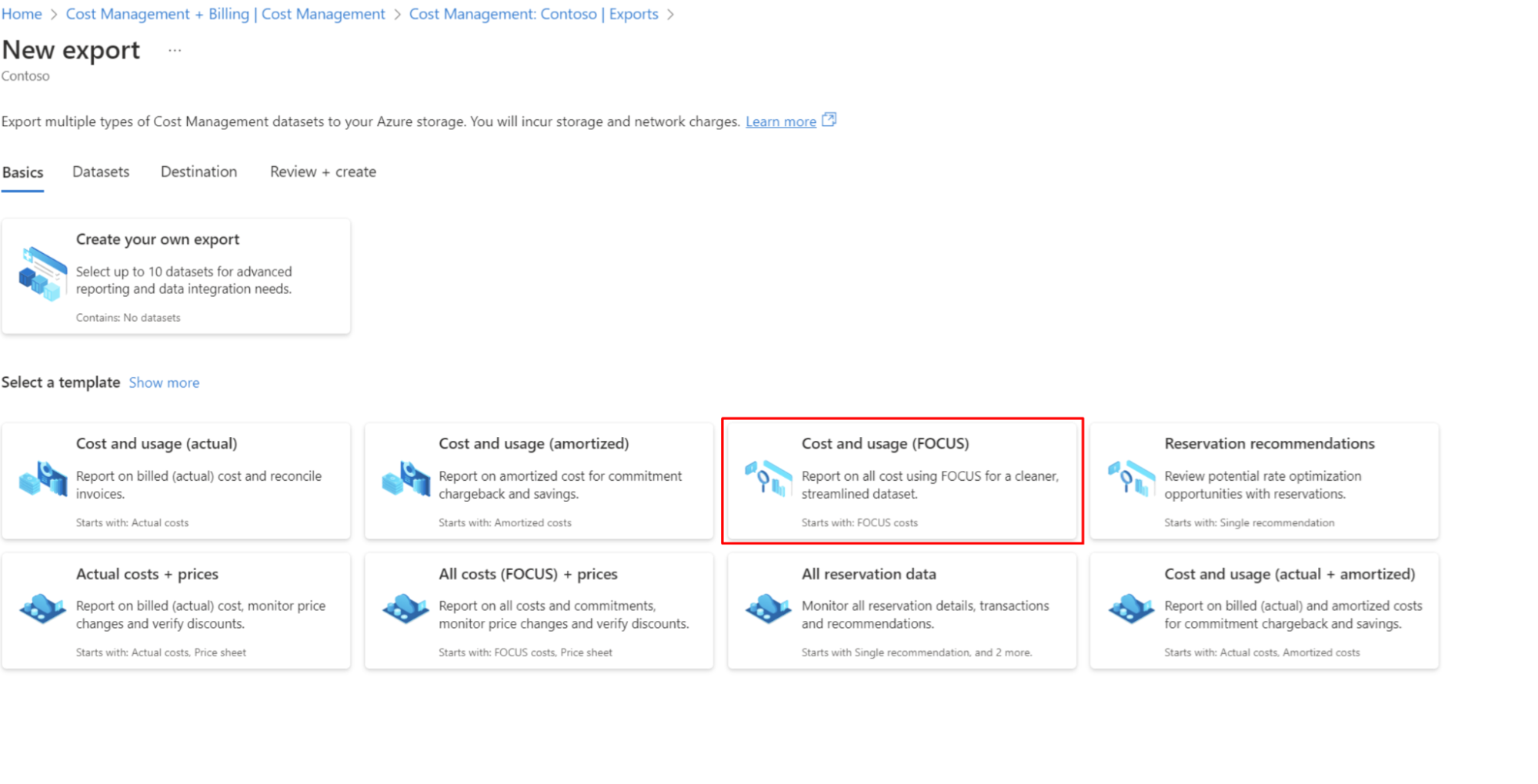
Create FOCUS Cost Export
- Go to Cost Management + Billing → Exports
- Make sure you're at the Billing Account scope, not a subscription scope
- Click Add
- Select FOCUS cost and usage (preview)
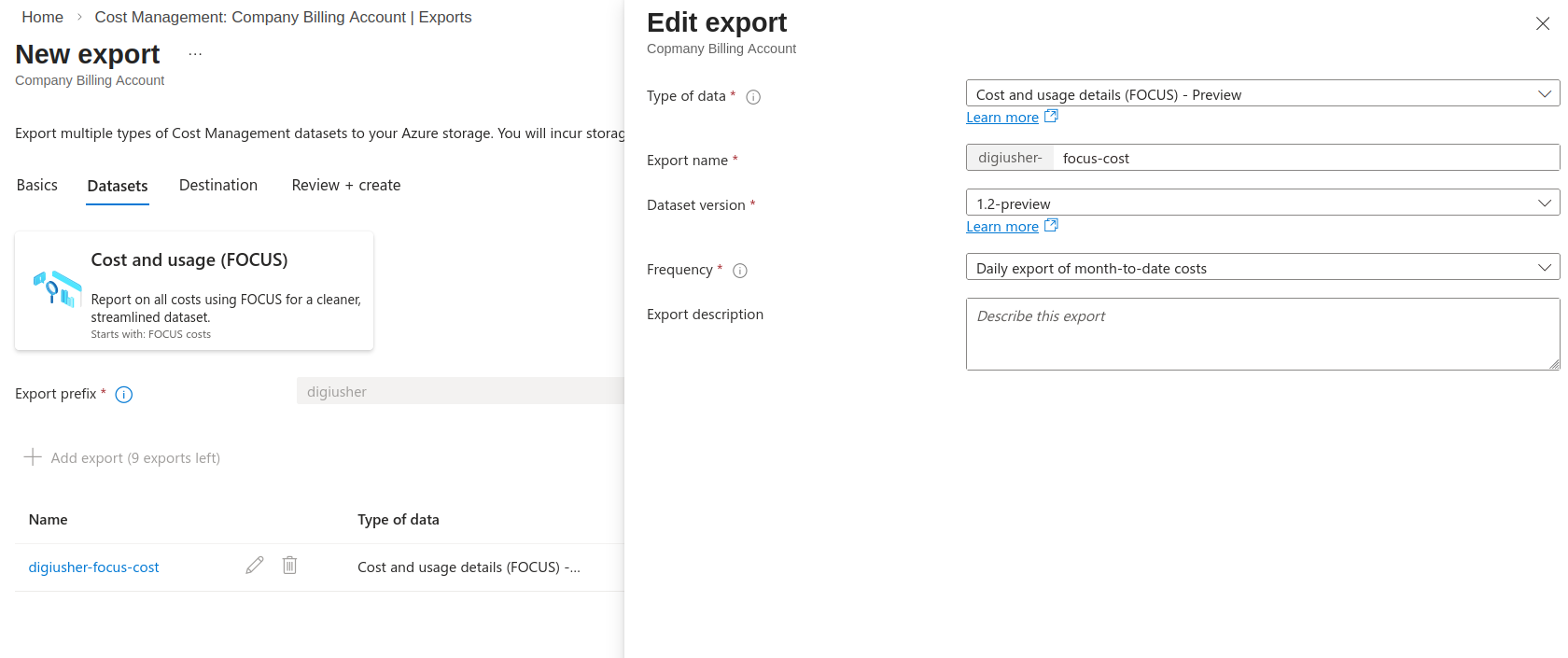
- Configure:
- Export name:
digiusher-focus-export - Frequency: Daily export of month-to-date costs
- Dataset version: 1.2-preview
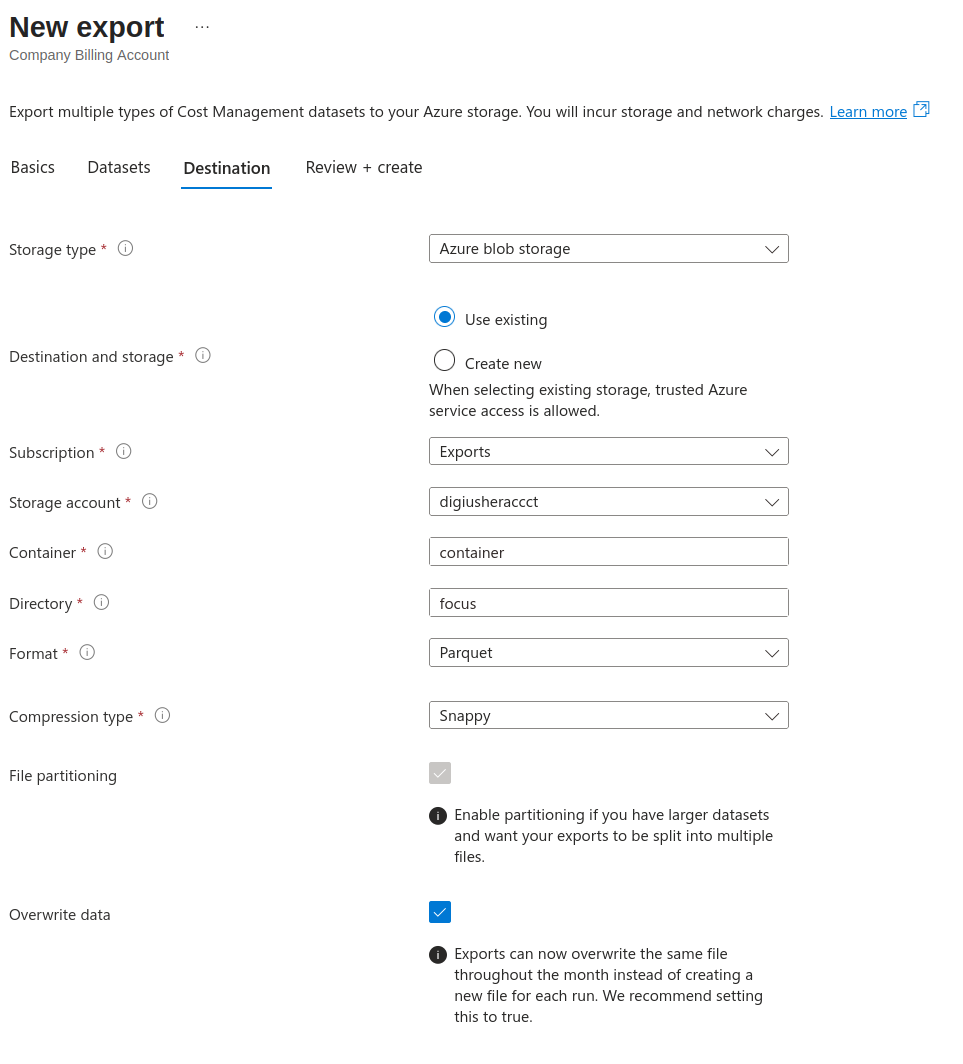
- File format: Parquet
- Compression: Snappy
- Export directory/path: focus
- Storage account: Select the account created in Step 4
- Container:
digiusher-focus-exports
- Export name:
- Click Create
Note
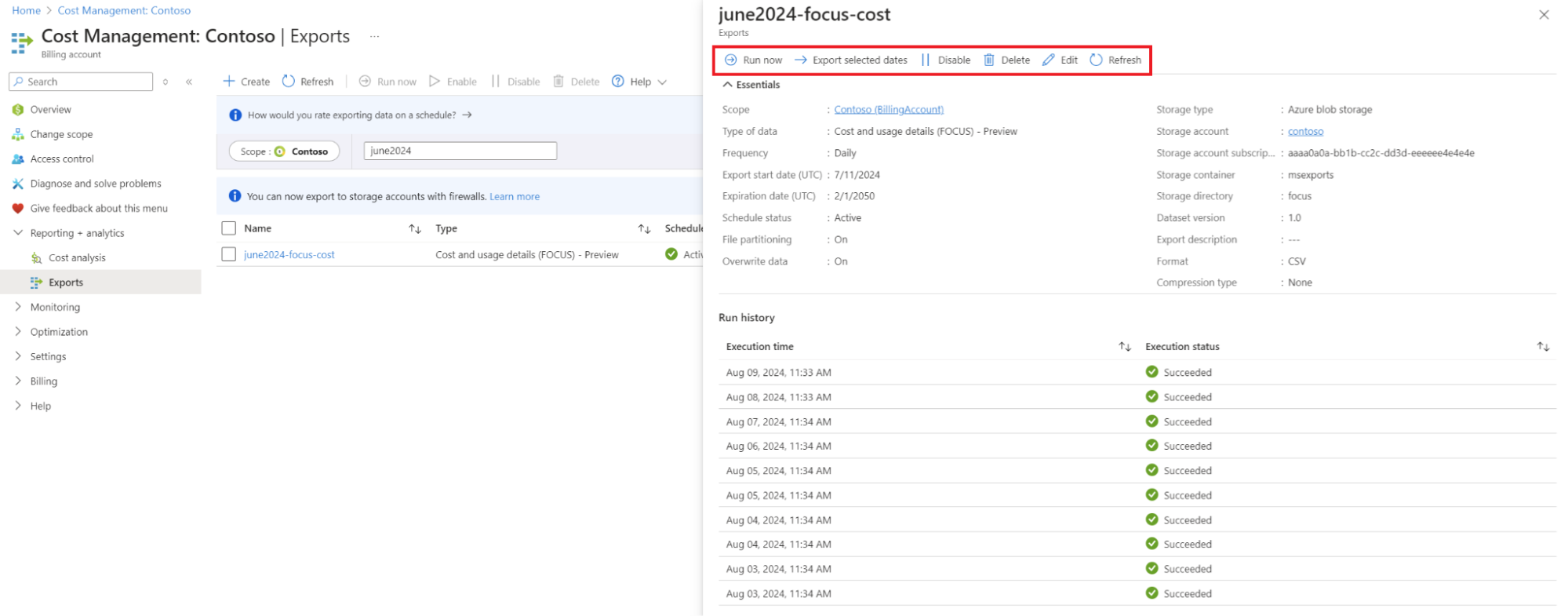
The first export will run within 24 hours. You can click "Run now" to trigger immediately.
Backfill historical data
- Go to Cost Management → Exports → select your export
- Click Export selected dates
- Run the export for each of the last 3 months (one at a time)
- Note that for large accounts you might have to wait for one export to finish before scheduling another month
(Optional) Reservations & Savings Plans Access
This step requires temporary elevated access to assign tenant-level roles.
6a. Enable Elevated Access
- Go to Azure Portal → Microsoft Entra ID → Properties
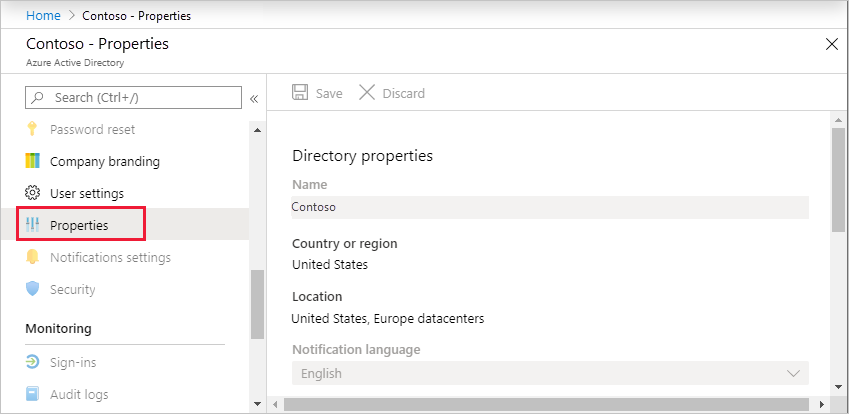
- Scroll to Access management for Azure resources
- Toggle to Yes
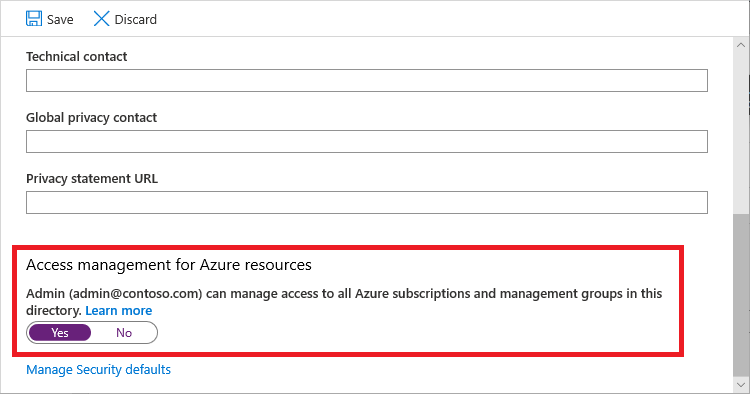
- Click Save
6b. Assign Reservations Reader
- Go to Reservations → Access Control (IAM) → Add role assignment
- Configure:
- Role:
Reservations Reader - Members:
DigiUsherApp
- Role:
- Click Review + assign
6c. Assign Savings Plan Reader
- Repeat the same process with role:
Savings Plan Reader
6d. Disable Elevated Access
- Go back to Microsoft Entra ID → Properties
- Toggle Access management for Azure resources to No
- Click Save
Important
Always disable elevated access after completing these assignments.
Connect in DigiUsher
After completing either the Terraform or Manual setup, enter the following into the DigiUsher platform to complete the connection:
| Field | Where to Find |
|---|---|
| Tenant ID | Azure Portal > Microsoft Entra ID > Overview, or terraform output tenant_id |
| Application (Client) ID | App Registration > Overview, or terraform output client_id |
| Client Secret | Created during App Registration setup, or terraform output client_secret |
| Storage Account Name | The storage account created for exports (e.g., digiusherexports<yourcompany>) |
| Storage Container Name | The container created inside the storage account (e.g., digiusher-focus-exports) |
| Export Root Path | The directory/path configured in the FOCUS export (e.g., focus) |
Verification Checklist
- App registration created with client secret
- Reader role assigned at Management Group (or Subscription) level
- Storage account and container created
- Storage Blob Data Reader role assigned on storage account
- FOCUS export created and scheduled
- (Optional) Reservations Reader and Savings Plan Reader assigned
- Elevated access disabled (if used)
-
*.digiusher.comallowlisted in network/firewall (if applicable) -
digiusher.comallowlisted for incoming email (if applicable)
Security
What DigiUsher CAN Access (Read-Only)
- Cost and usage data via FOCUS exports in Azure Storage
- Resource metadata (names, types, regions, tags) via Reader role
- Reservation and Savings Plan information (if optional access granted)
- Management Group, subscription, and resource group hierarchy
What DigiUsher CANNOT Do
- Create, modify, or delete any Azure resources
- Access application data, databases, or storage contents (beyond cost exports)
- Modify IAM policies or role assignments
- Read secrets, credentials, or encryption keys
- Access network traffic or logs content
- Make purchases or modify billing settings
Monitoring
Monitor App Registration activity in Microsoft Entra ID > Enterprise applications > DigiUsherApp > Sign-in logs and Audit logs.
Credential Rotation
- Terraform:
terraform apply -replace="azuread_application_password.digiusher" - Manual: App Registration > Certificates & secrets > New client secret (create new), then delete the old secret. Enter the new secret into the DigiUsher platform.
Revocation
- Terraform:
terraform destroy— removes the App Registration, all role assignments, and invalidates the client secret. - Manual: Delete the
DigiUsherAppApp Registration in Microsoft Entra ID > App registrations. This instantly invalidates the client secret and all associated role assignments.
Troubleshooting
Export not appearing
- Ensure
Microsoft.CostManagementExportsresource provider is registered - Go to Subscription → Resource providers → Search for CostManagementExports → Register
Permission denied on billing scope
- Verify you have EA Admin access
- Some EA accounts require the enrollment admin to grant access via the EA Portal first
Cannot see Management Groups
- Go to Management Groups → Start using management groups
- You may need to elevate access (Step 6a) to see the tenant root group
Need Help?
If you encounter any issues not covered above, contact us at support@digiusher.com and we'll help you get set up.
 DigiUsher Documentation
DigiUsher Documentation